To find out which key will get you in, search online for your laptop’s make and model along with the phrase “BIOS key.” Your computer will immediately restart, and instead of restarting and bringing you to your normal desktop screen, you’ll iphlpapi.dll be brought to a blue screen with a few options. You’re going to need to get to your BIOS menu so you can get to your TPM switch, and there are two ways to do that. The first is for much newer PCs, the second method for those a few years older. Regardless of which you choose, though, you’re going to need to restart your machine. So save any work and close any open windows or programs before proceeding.
- Windows system offers users one built-in protection tool – Windows Defender, which is designed to provide real-time protection for computer.
- The exported code will be in C#, even if it was originally written in a different language originally.Right-click on the DLL file in the Assembly Explorer.
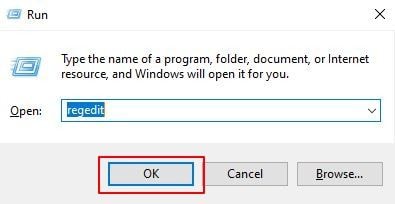
- When dealing with a Malware infested PC, you may have to delete several registry entries manually in case the cleanup tool you use does not remove all of them.
- At last, you can type exit to close Command Prompt and your computer will reboot.
Select both versions of the files and select Next. Again, select Uninstall on the new window and restart your PC when the operation reaches completion. Reinstalling the Visual C++ Redistributable resolved the problem for many Windows users in this Microsoft Community thread. Yes, I did re-publish, rebuilt, cleaned, etc. to no avail. However, I did notice that the hosting site has some IIS settings that I could tweak, I tweaked them and still problem not solved. It turns out that I was publishing to a particular folder within the root directory (purposely… to keep my apps in order) and once I published to the root directory, everything worked. However, I imagine the Web.config file, which is also in the root directory, must be the same for all apps, bummer.
They can also register themselves as BHOs to ensure an automatic execution each time the Internet Explorer browser is run. Once the task window opens, click the “processes” tab which will bring up an on-screen list of programs. Go through the list and select a file known as “wscript.exe.”. From the options received, click “end process”.
Since the system is unable to boot from the hard drive in this situation, correction of the problem often requires using the repair tools found on the Windows installation disc. This is usually caused by an illegal operation being performed. The only safe action the operating system can take in this situation is to restart the computer. As a result, data may be lost, as users are not given an opportunity to save it. This lookup tool helps solve the mystery of Windows error message codes, but its design leaves something to be desired. Simply enter the code number, and Error Message for Windows will display its description. You also can view the entire list of codes, numbering 0 to 10,112, which we like.
This was achieved by discovering and keeping track of all cells in registry hives to perform better validation, by processing cell slack space, and by discovering orphaned keys and values. Testing results closely matched existing registry forensics tools but with better validation and fewer false positives. In addition to transaction logs, we also examined methods for the recovery of deleted entries from registry hive files.
Insights Into Realistic Missing Dll Files Methods
I’d suggest including today’s date in the file name for easy reference. At the bottom of the export window, you have two options under Export Range. Although there is no substitute for a solid backup plan, it’s still a good idea to protect your system by creating a backup of your registry before making any changes to it. Individual keys, values, and value data can be deleted in this same process. Use the steps in this section to delete the registry item you created previously. Click the arrow next to HKEY_CURRENT_USER to close the branch of registry keys. This method can also be used to change existing data.
Insights On Simple Secrets Of Dll Files
It’s both a good and bad thing for a Windows machine. On the one hand, it can prevent certain classes of invasive malware from taking over your machine and is a core defense against ransomware. TPMs are controversial among security specialists and governments. An updated and enabled TPM is a strong preventative against firmware attacks, which have risen steadily and drawn Microsoft’s attention. However, it also allows remote attestation and may restrict the kinds of software your machine is allowed to run. TPM-equipped machines generally aren’t shipped in countries where western encryption is banned. China uses its state-regulated alternative, TCM.
